What I want to do!
I am using a mini PC "Cubietruck / Cubieboard 3" as server for DocBox and a Raspberry Pi 3 for home-automation with Openhabian. Now I have the LoRa-Node (Server) on an ESP8266. I want to run it all on one system and have some peace for the next years. I think Raspberry is a good platform with long maintenance and good support.
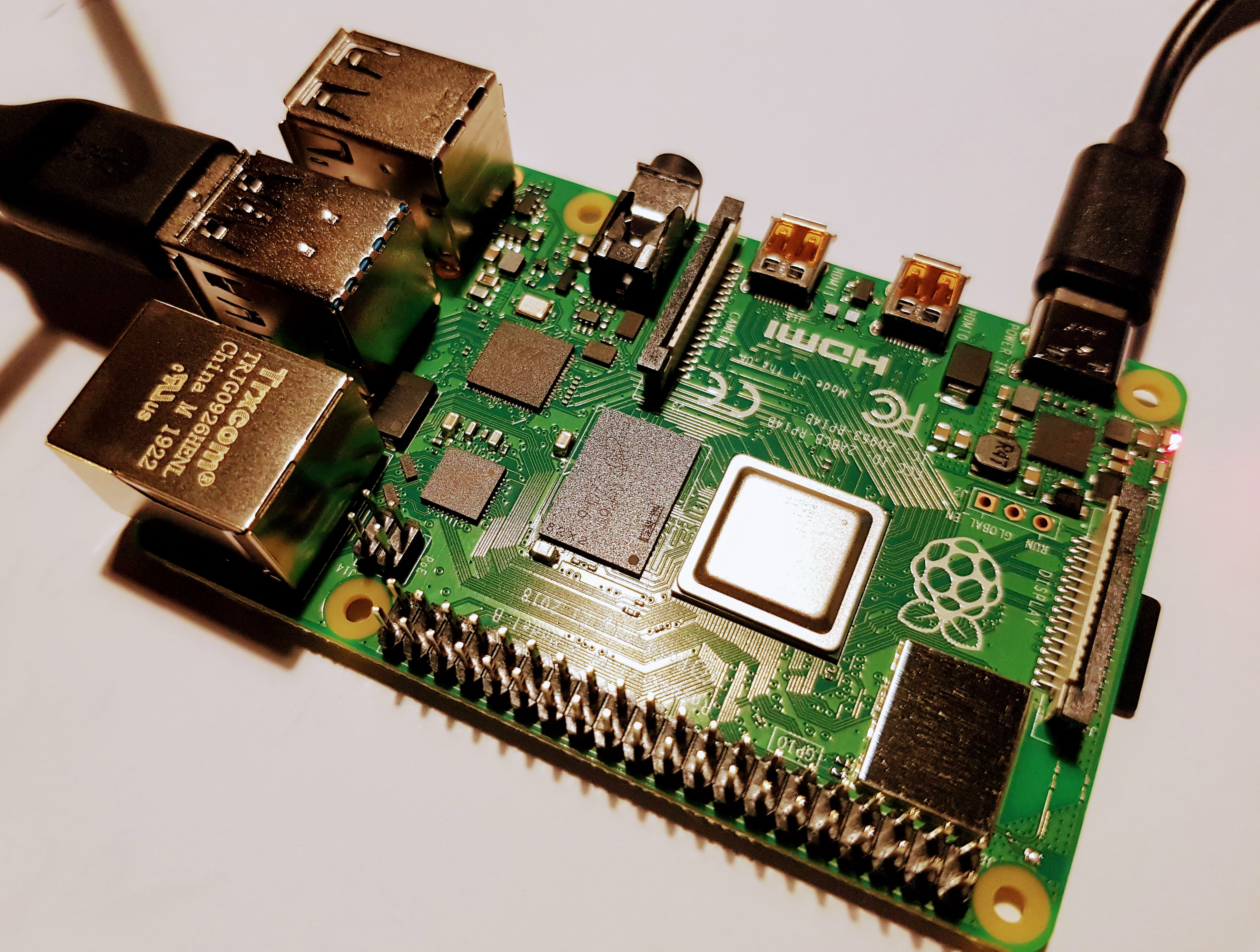
Setting up the RPI-4
Components:
- RPI4 with 4 GB Ram (the best version)
- Samsung SSD T5 500 GB
- dezen USB Charger
Installation
Prepare SD Card
I want to directly install Raspbian and on initial boot access it via SSH (no HDMI needed). For this SSH and WLAN have to be configured on the boot SD card.
Download latest Raspbian Buster Lite
Copy it to SD Card (e.g. for linux using Etcher) and manipulate the SD card folder and files on your linux PC before inserting into the RPI as follow:
1) Enable SSH: Place a file named 'ssh', without any extension, onto the boot partition of the SD card
2) Enable remote-login with su, edit: //etc/ssh/sshd_config and set PermitRootLogin yes
3) Update WIFI Configuration /etc/wpa_supplicant with following:
ctrl_interface=DIR=/var/run/wpa_supplicant GROUP=netdev
update_config=1
country=DE
network={
ssid="your-ssid"
psk="you-pwd"
}
Boot from USB
New RPI can not yet boot directly from USB, but can be "tricked" by give him the SD card for boot, and set the SSD as root folder. A really good description can be found here:
https://www.tomshardware.co.uk/boot-raspberry-pi-from-usb,news-61081.html
Security and Login via SSH
Connection to the Pi goes via SSH, to avoid typing in the PWD each time - we use SSH keys. For testing purpose the PI runs on SSH-Keyfile without passphrase question (less secure, but its only for a test-system). I also have another SSH-Keyfile (for other purposes) with a passphrase, so I need to create a new SSH-Keyfile only for the PI.
Concept: The PI will contain a file "authorized_keys" that has a list of *trusted* clients that can connect via SSH. The client will generate a key-pair and copy his public-key to the PI "authorized_key". On authentication the client will use his private-key to prove that he own the public-key.
On PI - first create a new user:
sudo adduser username
sudo usermod -aG sudo username
Log-Off and Log-In with new user via SSH and PWD - to prepare the ssh folder. It will contain a file with public keys of authenticated servers that can login into the PI.
cd ~
mkdir .ssh
chmod 700 ~/.ssh
On your PC (descriptions are for Linux/Ubuntu) edit the file ~./ssh/config. Each line is one key-file use (Tip from Stackoverflow)
IdentityFile ~/.ssh/id_rsa
IdentityFile ~/.ssh/id_rsa_pi
Generate a new key-file via ssh-keygen, make sure to use the file-name from above and copy the file to the authorized_keys of the PI with
ssh-copy-id -i ~/.ssh/id_rsa_pi new_user@pi
Login into the PI from the PC should now be possible just with ssh user_name@pi.